What are the primary requirements of information security

Ava Hall
Updated on April 15, 2026
The fundamental principles (tenets) of information security are confidentiality, integrity, and availability.
What are the three primary requirements of information security?
The weight given to each of the three major requirements describing needs for information security—confidentiality, integrity, and availability—depends strongly on circumstances.
What are the primary requirements of information security quizlet?
The 3 primary goals of information security are Confidentiality, Integrity and Availability, also known as the CIA triad.
What are information security requirements?
- Access, Authentication, and Authorization Management.
- Awareness, Training, and Education.
- Disaster Recovery Planning and Data Backup for Information Systems and Services.
- Electronic Data Disposal and Media Sanitization.
- Encryption.
- Information Security Risk Management.
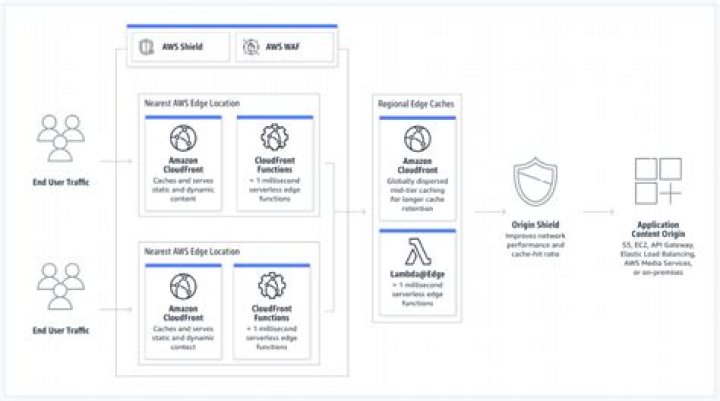
- Network Security.
What are the primary objectives of information security?
Security of computer networks and systems is almost always discussed within information security that has three fundamental objectives, namely confidentiality, integrity, and availability.
What is CIA triad in cyber security?
Confidentiality, integrity and availability, also known as the CIA triad, is a model designed to guide policies for information security within an organization. The model is also sometimes referred to as the AIC triad (availability, integrity and confidentiality) to avoid confusion with the Central Intelligence Agency.
What are the four elements of security?
- Protection, Detection, Verification & Reaction.
- ‘Protection’ is the physical barrier, such as walls and fences, which separates your property from the rest of the world.
Why are security requirements important?
Implementing information security requirements allows your business to be more prepared for the security threats that you and your customers are facing, and ensures that you can defend against advanced security threats that are endangering your business.Why is information security required?
Reducing the risk of data breaches and attacks in IT systems. Applying security controls to prevent unauthorized access to sensitive information. … Ensuring business continuity through data protection of information assets. Providing peace of mind by keeping confidential information safe from security threats.
What is meant by information security?Information security is a set of practices designed to keep personal data secure from unauthorized access and alteration during storing or transmitting from one place to another.
Article first time published onWhat are the primary goals of information security management quizlet?
B. The primary goals and objectives of security are confidentiality, integrity, and availability, commonly referred to as the CIA Triad .
What is information security quizlet?
Information Security. The protection of information and information systems from unauthorized access, use, disclosure, modification, disruption, removal or destruction.
What is an information security policy quizlet?
Information Security Policies. Written instructions provided by management that inform employees and others in the workplace about proper behavior regarding the use of information and information assets.
What are the 5 components of information security?
It relies on five major elements: confidentiality, integrity, availability, authenticity, and non-repudiation.
What are the characteristics of information security?
The fundamental principles (tenets) of information security are confidentiality, integrity, and availability. Every element of an information security program (and every security control put in place by an entity) should be designed to achieve one or more of these principles. Together, they are called the CIA Triad.
What are the 3 security domains?
Confidential, Secret, and Top Secret are three security domains used by the U.S. Department of Defense (DoD), for example.
What are the basic security requirements of a typical SSO solution?
- It should be written either in java,.net PHP or cobol since no other language/platform are secure enough to provide a sso solution.
- The “SSO Token” used for SSO should be secured against theft, spoofing or forgery.
- it should eliminate calculation of user password to multiple applications/systems to gain access to them.
What are security requirements application?
A security requirement is a goal set out for an application at its inception. Every application fits a need or a requirement. For example, an application might need to allow customers to perform actions without calling customer service.
What are the three main objectives of information security select the best answer?
Information Security programs are build around 3 objectives, commonly known as CIA – Confidentiality, Integrity, Availability. Confidentiality – means information is not disclosed to unauthorized individuals, entities and process.
Which of the following describes the primary goal of the CIA approach to information security management?
The goal of information security management is to enhance the confidence, integrity and authority (CIA) of a firm’s information.
What are the steps of the information Security Program Lifecycle?
- Step 1: Identify. The first step in the information security program lifecycle is to identify what items need to be protected. …
- Step 2: Assess. …
- Step 3: Design. …
- Step 4: Implement. …
- Step 5: Protect. …
- Step 6: Monitor.
What is required to access classified information Select all that apply?
In order to have authorized access to classified information, an individual must have national security eligibility and a need- to-know the information, and must have executed a Standard Form 312, also known as SF-312, Classified Information Nondisclosure Agreement.
Which best describes SCI?
Sensitive Compartmented Information (SCI) is a classification label that is put on data and information that is sensitive in nature and belongs to a certain program or department. The data can be derived from multiple sources as Critical Program Information (CPI), analysis data and/or intelligence data.
What is information security policy why it is critical to the success of the information security Program?
It is designed to provide structure in the workplace, create a productive and effective work place. It is free from unnecessary distractions. Critical to the success of the InfoSec program: InfoSec is to protect the Information of workers and customers; it is difficult to maintain this policy in an organization.
Why are information security policies important to an organization quizlet?
The Information Security Policy sets out strategies for employees and employer so that each is aware of security expectations. It is important because it helps employees to understand the direction and needs of the organization. … Security policies are inexpensive but difficult to implement.
What is bulls eye model?
The bull’s-eye model is an implementation model in which information security issues are addressed from the general to the specific, always starting with policy.
What is a main component of information security?
The basic components of information security are most often summed up by the so-called CIA triad: confidentiality, integrity, and availability.
What are the 6 components of information system?
Hence, information systems can be viewed as having six major components: hardware, software, network communications, data, people, and processes.